All articles containing the tag [
Local Compliance
]-
Network Security Reinforcement And Compliance Recommendations For Deploying Servers In Cambodia (CN2) That Connect Back To Domestic Networks In China
Cybersecurity reinforcement and compliance recommendations for deploying servers in Cambodia that connect back to China, covering practical strategies such as compliance assessments, link and routing optimization, firewalls, DDoS protection, host hardening, log auditing, and cross-border data compliance.
Cambodia CN2: Home Country Server Network Security Compliance DDoS Protection Data Encryption Log Auditing Cross-border Transmission and Localization Compliance -
Network Security Reinforcement And Compliance Recommendations For Deploying Servers In Cambodia (CN2) That Connect Back To Domestic Networks In China
Cybersecurity reinforcement and compliance recommendations for deploying servers in Cambodia that connect back to China, covering practical strategies such as compliance assessments, link and routing optimization, firewalls, DDoS protection, host hardening, log auditing, and cross-border data compliance.
Cambodia CN2: Home Country Server Network Security Compliance DDoS Protection Data Encryption Log Auditing Cross-border Transmission and Localization Compliance -
Common Misunderstandings And Pitfall Avoidance Guide When Purchasing Malaysian Server Letter Combinations
this article analyzes common misunderstandings and pitfall avoidance guidelines for malaysian server letter combinations to help enterprises correctly understand letter coding, verification locations and compliance requirements when purchasing and deploying, thereby reducing operational risks.
malaysia servers monogram buying misunderstandings pitfall avoidance guide data center geographical location latency compliance -
How A Small Entrepreneurial Team Can Quickly Make Decisions Among Many Vietnamese Cloud Server Brands
a practical decision-making framework and implementation steps for small entrepreneurial teams to choose cloud servers in the vietnamese market, including demand identification, assessment dimensions, pilot verification, operation and maintenance support, and migration suggestions to facilitate rapid implementation.
vietnam cloud server small entrepreneurial team local cloud service provider cloud deployment cloud host vietnam market cloud selection -
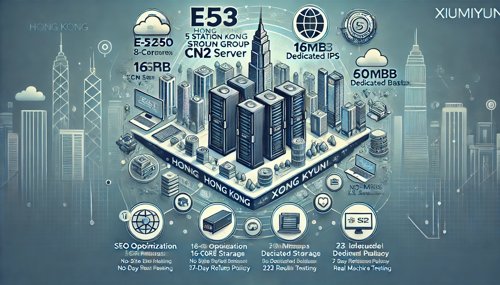
This Technical Requirements List Outlines The Connection And Monitoring Specifications Prepared For The Hong Kong Cloud Hosting Data Center Proxy
This document outlines the technical requirements for access and monitoring solutions designed for Hong Kong-based cloud hosting data centers. It covers key aspects such as network connectivity, bandwidth redundancy, physical access, power supply infrastructure, permission management, performance monitoring, and log auditing, facilitating compliant implementation and operational maintenance.
Technical Requirements List for Monitoring Access via Proxy in Hong Kong Cloud Hosting Data Centers: Network Bandwidth Redundancy Security Log Monitoring and Alarm Functions -
Build A V Club Hong Kong Server From Scratch To Support Multiplayer Connections And Management Strategies
build a v club hong kong server from scratch, covering location selection, network and hardware configuration, installation and deployment, multiplayer online performance optimization, security management and operation and maintenance strategies. it is a practical guide for operation and maintenance engineers and community administrators.
v society hong kong server hong kong game server multiplayer online server management game console deployment geo optimization -
Recommended Security Protection Plan To Protect Hong Kong Site Group From Malicious Attacks After Establishment
recommended security protection solutions for the hong kong site group after establishment, covering the network layer, application layer, access control and operation and maintenance compliance, helping to reduce the risk of malicious attacks and improve availability and compliance.
hong kong site group security protection plan site group construction website security ddos protection waf cdn log monitoring data backup -
Comparative Analysis Of The Advantages And Disadvantages Of Taiwan Time Server Deployed In The Cloud Versus Locally
this article conducts a professional comparative analysis of the advantages and disadvantages of deploying taiwan time servers in the cloud and locally, covering latency, availability, security compliance, cost maintenance and applicable scenarios, and provides implementation suggestions and best practices.
taiwan time server time server ntp cloud deployment local deployment clock synchronization delay availability security compliance hybrid deployment -
The Role Of Regular Detection And Vulnerability Scanning In Preventing Cambodian Servers From Being Attacked By Hackers
discuss the role of regular detection and vulnerability scanning in preventing cambodian servers from being attacked by hackers, covering threat types, scanning methods, implementation strategies and response processes, and providing practical security suggestions.
cambodia servers vulnerability scanning regular detection hacker attack protection network security cambodiaservers security detection